-
Products & Services
-
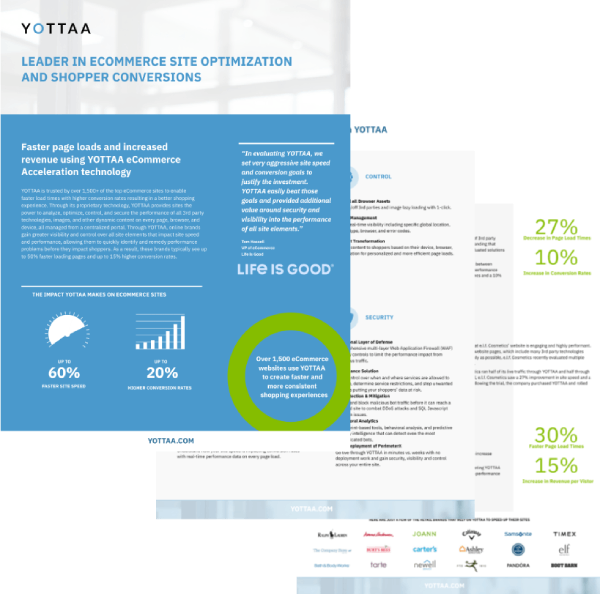
CapabilitiesWeb Performance CloudOptimize
Streamline third-party loading
Dynamically cache content in the browser
Make your site user-specific
MonitorMonitor your users in real-time
Track your Core Web Vitals metrics
Compare site performance with peers
Know what tech is on your site
Mitigate errors before they impact shoppers
Quantify site speed optimizations
Proactively identify performance issues
-
Resources
Sorry, the page you are looking for is no longer available!
We do have similar content available on our Resource page and Blog posts.
Company
Learn
Contact
- 333 Wyman Street, Suite 200 Waltham, MA 02451
- Email: info@yottaa.com
- Phone: (877) 767-0154
Signup for Free Web Performance Tips & Stories
Copyright© 2025 Yottaa • Privacy Policy • Acceptable Use Policy • Cookie Policy